Modern organizations run on laptops, phones, cloud apps, and remote access tools. Every connected device becomes a potential doorway for cyber threats. That reality makes endpoint security a core priority for companies of every size.
This endpoint security solutions guide explains how advanced protection works, why it matters, and how to choose the right system for long term resilience.
What Is Endpoint Security?
Endpoint security is a cybersecurity approach focused on protecting user devices such as desktops, servers, tablets, and smartphones. Each device acts as an endpoint within a business network.
Instead of relying only on perimeter firewalls, this model secures every access point individually. If one device becomes compromised, strong controls prevent attackers from spreading across the environment.
Why Endpoint Protection Matters Today
Remote work, cloud services, and mobile computing have expanded the attack surface. Traditional antivirus tools are no longer enough.
Modern threats include:
- Ransomware
- Phishing campaigns
- Fileless malware
- Zero day exploits
- Insider misuse
A strong security strategy detects suspicious behavior, isolates infected systems, and blocks unauthorized activity before damage spreads.
Core Components of Endpoint Security Solutions
1. Next Generation Antivirus (NGAV)
Unlike legacy antivirus tools, NGAV uses behavioral analysis and machine learning to stop unknown threats. It identifies patterns instead of relying only on known signatures.
2. Endpoint Detection and Response (EDR)
EDR continuously monitors devices for unusual actions. When suspicious behavior appears, the system alerts administrators and provides investigation tools.
3. Extended Detection and Response (XDR)
XDR expands visibility across email, cloud workloads, and network traffic. It correlates data from multiple sources for faster threat containment.
4. Device Control
This feature manages USB drives, external storage, and removable media to reduce data loss risks.
5. Encryption and Data Protection
Built in encryption protects sensitive information even if a device is lost or stolen.
Leading Endpoint Security Platforms
1. CrowdStrike
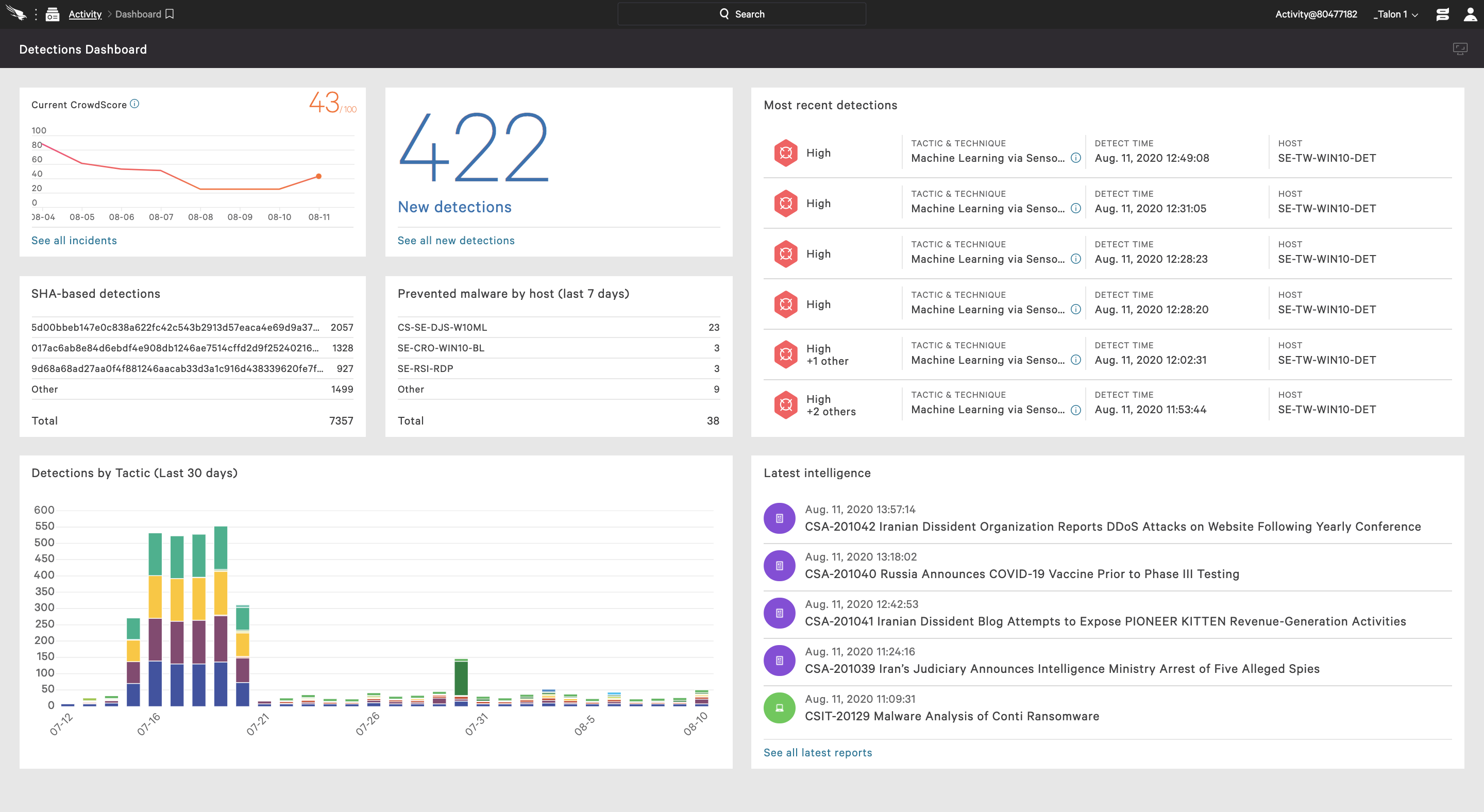
CrowdStrike offers a cloud native platform with AI driven threat intelligence. Its Falcon system combines NGAV, EDR, and threat hunting in a single lightweight agent.
2. Microsoft Defender for Endpoint
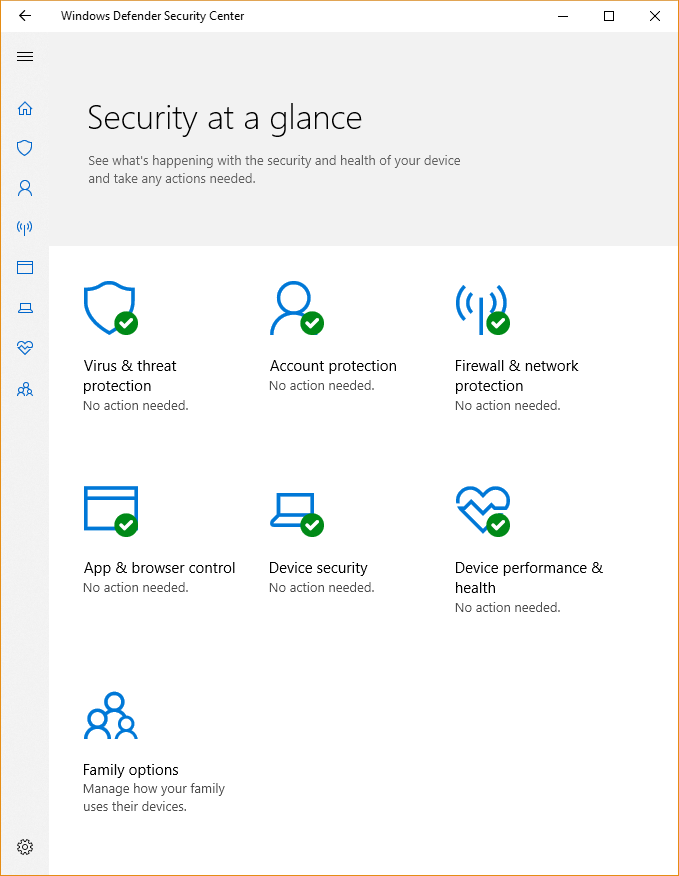
Microsoft Defender integrates deeply with Windows environments. It delivers real time monitoring, automated investigation, and vulnerability management.
3. SentinelOne
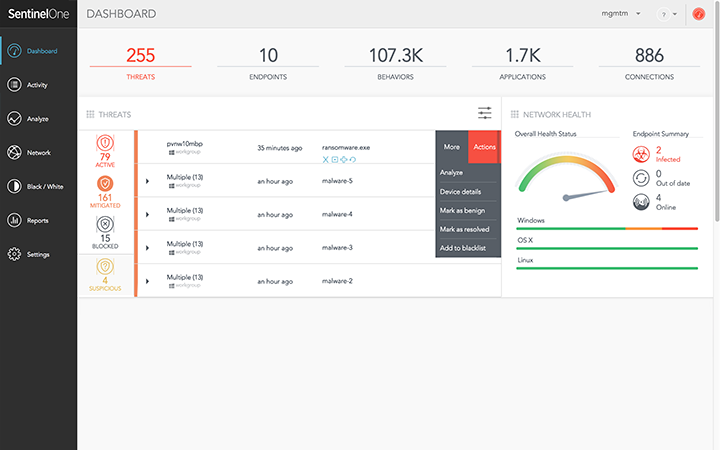
SentinelOne uses autonomous AI to prevent, detect, and respond to malicious activity without heavy manual intervention.
4. Sophos Intercept X
Sophos delivers layered defense with deep learning malware detection and anti ransomware capabilities.
Key Benefits of Modern Endpoint Security
- Centralized visibility across all devices
- Faster threat detection
- Reduced downtime from attacks
- Automated remediation
- Regulatory compliance support
These advantages strengthen digital resilience while lowering operational risk.
How to Choose the Right Endpoint Security Solution
When evaluating tools, focus on:
- Scalability for remote teams
- Cloud native architecture
- Real time response automation
- Integration with existing systems
- Transparent reporting and analytics
A proper assessment ensures your organization gains both protection and performance without unnecessary complexity.
Best Practices for Stronger Endpoint Security
- Enforce multi factor authentication
- Keep operating systems updated
- Apply least privilege access controls
- Conduct regular security awareness training
- Monitor continuously, not periodically
Technology alone is not enough. Processes and employee awareness complete the defense strategy.
Final Thoughts
Cyber threats evolve quickly, targeting weaknesses at the device level. A comprehensive endpoint security approach protects each connected system, reduces exposure, and keeps business operations stable.
Investing in modern endpoint security solutions is not optional. It is a strategic necessity for organizations that depend on digital infrastructure every day.