Phishing prevention is no longer optional. Every inbox, login page, and mobile device is a potential entry point for cybercrime. Attackers refine tactics daily, using realistic branding, urgency, and social engineering to trick even experienced users.
This guide explores phishing prevention techniques that reduce risk, protect data, and strengthen organizational resilience. Each section includes practical steps you can apply immediately.
1. Recognize Deceptive Messages Early

The first layer of phishing prevention starts with awareness. Fraudulent emails often create panic or excitement. They may claim account suspension, prize winnings, or urgent verification.
Warning signs include:
- Mismatched sender domains
- Spelling inconsistencies
- Suspicious attachments
- Links that redirect to unfamiliar addresses
Hover over hyperlinks before clicking. Verify unusual requests directly through official websites instead of embedded buttons.
2. Strengthen Authentication Layers

Strong credentials are critical in phishing prevention techniques. Even if passwords are exposed, extra verification steps block unauthorized access.
Best practices include:
- Multi factor authentication
- Hardware security keys
- Biometric login
- Password managers for unique credentials
Avoid reusing the same login details across platforms. Compromised information from one service can unlock many others.
3. Train Teams Continuously

Human behavior often determines success or failure in phishing prevention. Regular training builds instinctive caution.
Effective programs include:
- Simulated attack campaigns
- Interactive workshops
- Real case study reviews
- Clear reporting procedures
Encourage employees to report suspicious communication without fear of blame. Early reporting limits spread.
4. Deploy Advanced Email Filtering
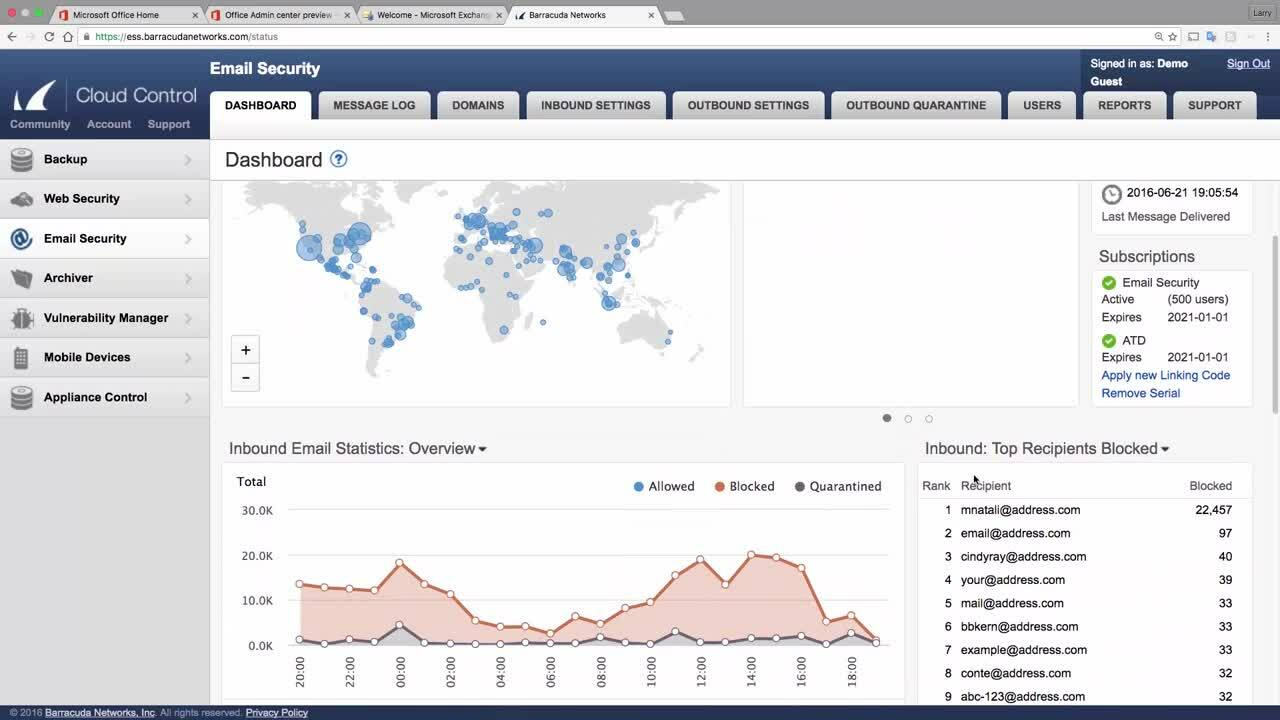
Technology strengthens phishing prevention techniques at scale. Modern filtering systems analyze sender reputation, attachments, and embedded URLs before delivery.
Consider implementing:
- Secure email gateways
- Domain authentication protocols
- Anti malware scanning
- Real time threat intelligence feeds
Layered defenses reduce reliance on individual judgment alone.
5. Protect Mobile and Remote Devices

Remote work expands exposure. Smartphones, tablets, and personal laptops often lack corporate safeguards.
Improve phishing prevention by:
- Installing device management solutions
- Enforcing encrypted connections
- Updating operating systems promptly
- Restricting downloads from unknown sources
Public WiFi networks increase vulnerability. Use secure connections whenever possible.
6. Monitor and Respond Quickly

Even strong phishing prevention cannot eliminate every attempt. Rapid detection and response minimize damage.
Create a response framework that includes:
- Immediate credential resets
- Account activity audits
- Malware scans
- Notification procedures
Document lessons learned after each incident. Continuous improvement strengthens resilience.
Final Thoughts
Phishing prevention techniques combine awareness, authentication, filtering, and rapid response. No single tool guarantees safety. Instead, a layered strategy reduces exposure and protects sensitive information.
Cyber threats evolve. Regular updates, employee education, and smart technology choices ensure your defenses stay effective. When prevention becomes routine rather than reactive, organizations stay one step ahead of digital deception.